In each analytical report based on the work of our MDR team, there is a section “Nature of Critical Incidents” where we share the distribution of types of critical incidents by industry. And sometimes we even allow ourselves cautious analytics — like the fact that the Government sector is most often subject to human-led attacks, both for espionage and for sabotage. And Financial institutions, despite more mature (on average) approaches to ensuring information security, often become victims for the obvious reason of potential financial gain for attackers.
In addition, starting from 2021, there is a stable growth in the compromise of infrastructure through trusted suppliers of solutions and/or services — since this is often easier than hacking through the perimeter with subsequent unnoticed passage through the echeloned defense of a high-maturity corporation (although such scenarios also make it into the top-5 every year).
It’s also easy to notice the connection between the cyber threat landscape and the political situation in the world; many conflicts begin in cyberspace and only later receive their reflection on the political map of the world. Such a connection can be seen when analyzing the change in the nature of high-critical incidents over the years, which was also shown based on our annual reports.
But no less interesting observations can be made if we track the change in the nature of high-critical incidents by industry. That’s what we’ll talk about in this study.
Critical Incidents in 2025#
The share of high-critical incidents is currently small: in 2025, it was less than 4% of the total number of MDR incidents. If we look at the history of changes in incidents by criticality over different years, the picture will be as follows.
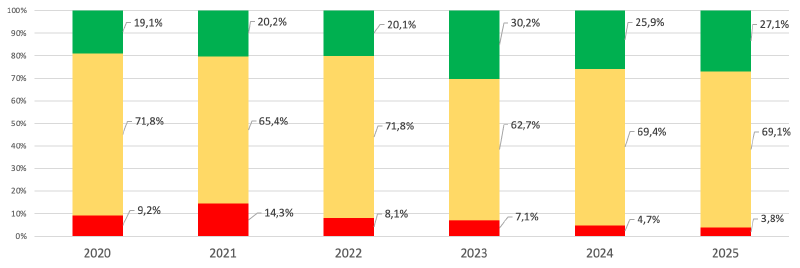
There was a surge in the share of high-critical incidents in 2021, its nature became clear in 2022. But then — a stable decline. We’ve already analyzed this surge several times, so let’s move on.
Let’s focus exclusively on high-critical incidents — and see what share of the total number of critical incidents each type occupied in 2025, broken down by industry:
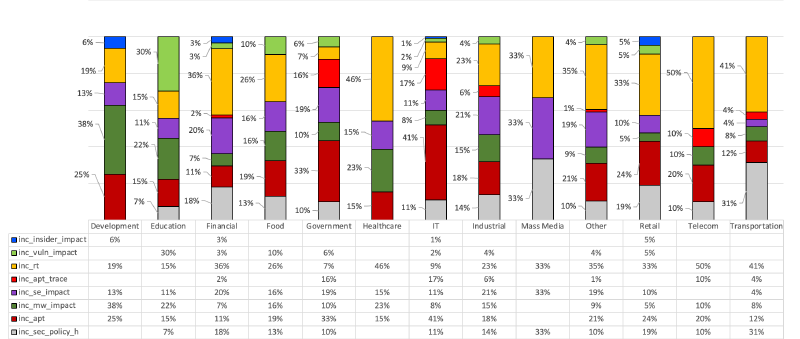
From this statistics, we can learn who conducted more cyber exercises (inc_rt) or who had more “suspicious activity from legitimate accounts without visible signs of hacking, but without confirmation that these are insiders” (inc_sec_policy_h).
But our goal is to analyze the cyber threat landscape, and it has a very indirect reflection in the share of penetration tests and cyber exercises. And it cannot depend on the customer’s confirmation of insider attacks (and MDR is not the most effective tool for detecting insiders).
In addition, it’s worth removing from consideration attacks on denial of service (which were not noticed in MDR statistics for 2025, but were encountered earlier), as well as the inc_vuln_impact item - detection of critical vulnerabilities (since MDR also loses in effectiveness to specialized means).
Having removed what does not characterize the threat landscape and what MDR cannot provide an objective picture of, we get the following layout for 2025:
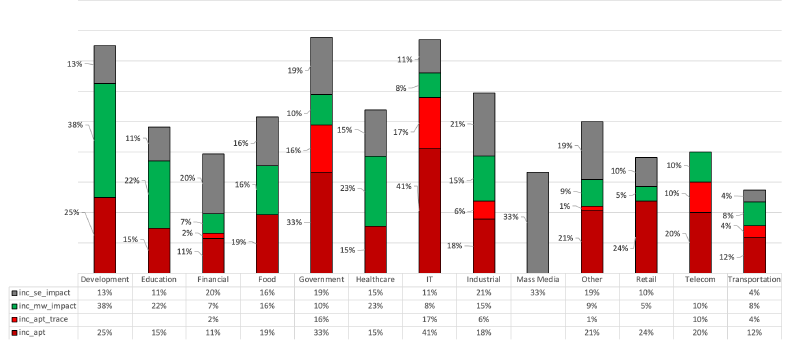
It follows from the picture that every third critical incident in the Media was a “successful social engineering” (inc_se_impact). Interestingly, the remaining two-thirds were divided between “confirmed insider work” (inc_insider_impact) and “penetration test” (inc_rt).
At the same time, IT companies outpaced the traditional leader, the Government sector, in the number of human-driven attacks (inc_apt): 41% versus 33%. Moreover, the share of past human-driven attacks (inc_apt_trace: detection of human-managed attack artifacts, but no active actions by the attacker were observed at the time of detection) in the IT sector also outpaced the government sector: 17% versus 16%.
At first glance, it’s curious that human-led attacks were often observed in Developers — in every fourth case (25%). However, the situation is explained by the first place of Development in the number of critical malware attacks (38%). Since modern ransomware attacks start as human-operated, it can be argued that these two shares reflect the same attacks, but detected and stopped in MDR at different stages. In such cases, detection at the stage of active actions by the attacker (inc_apt) is significantly more attractive, since by the time the ransomware is launched (inc_mw_impact), the network is already fully compromised, and the chances of successful response are low.
This situation is common for all industries where attackers are interested in disrupting work — including Industry, Transport, Healthcare, and Educational institutions. For Education and Healthcare, the goal of attackers is also personal data, a similar goal is pursued in attacks on Retail.
Human-Driven Attacks#
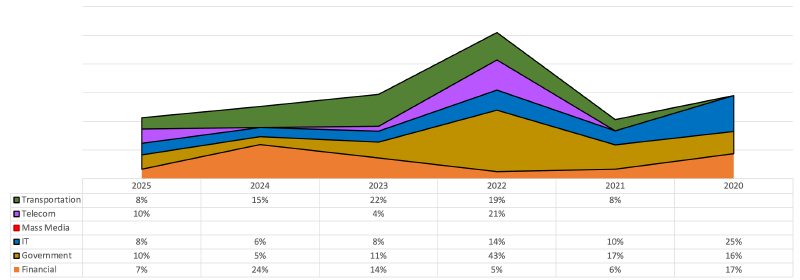
It’s interesting to look at how the priorities of human-operated attacks changed over time. To simplify the analysis, let’s consider only the following industries: Transport, Telecom, Media, IT, Government, Finance.
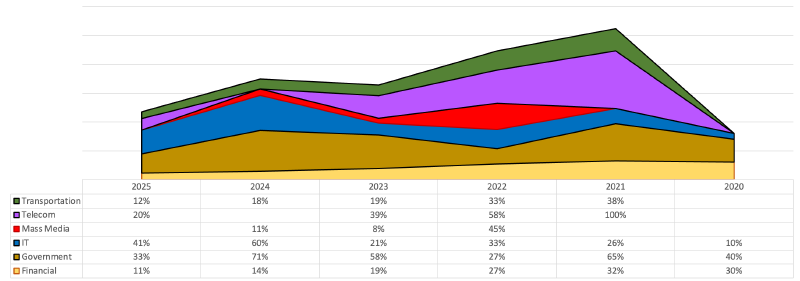
From the presented visualization, we can make the following observations:
In Finance, there is always some share of human-led attacks. The largest share was observed in 2020 and 2021, but since then, there has been a stable decline.
In Government institutions, the share of human-driven attacks is most significant. The first surge (65%) was in 2021, the second (71%) — in 2024. In 2022, a relatively large (up to 27%) decline in activity was noted, but in other industries, on the contrary, there was growth.
In the IT sector, since 2020, there has been a stable growth in the share of human-driven attacks, and their share by volume is approaching the situation in the Government sector, which is direct confirmation of the growing popularity of attacks on the supply chain, which we also see in the news.
All attacks on Telecoms in 2021 were human-led, and the most likely goal was the exploitation of trusted relationships in the following year, 2022. But since then, there has been a decline, with a simultaneous growth in IT, which was especially contrast in 2024, where the share in telecoms was 0%, and in IT - 60%. Apparently, the effectiveness of attacks on the supply chain is higher, and they are crowding out trusted relationships.
The Media forms public opinion, so they were particularly affected in 2022 — despite the fact that in 2020 and 2021, there was no attackers’ interest in them at all. However, in subsequent years, the interest of attackers in this industry has significantly decreased again: in 2025, they returned to the level of 2020-21.
The share of human-managed attacks on Transport companies remains low. The highest level was observed in 2021 (38%) and 2022 (33%), but since then — a slight decline, but not to zero, like in the media.
Malware Attacks#
We previously noted that human-driven attacks and malware attacks often represent the same incident, detected at different stages. Therefore, it’s interesting to look at high-critical malware attacks by sector:
The Financial sector is stably attacked with malware, but the most affected was in 2024 (24%). And in 2021 and 2022, there was a decline; apparently, attackers focused on more priority areas.
One of such priority sectors was the Government sector: in 2022, such institutions were most affected — 43% of critical malware attacks. In the 2022 report, the T1078 technique was noted in the top-3, which is a consequence of exploiting trusted relationships (most likely, on the part of Telecoms, which were compromised as early as 2021).
The fact that Telecoms were compromised in 2021 is also evidenced by the high share of malware attacks on this sector in 2022 (21%). Especially considering that in 2023, such attacks were only 4%, and in 2025, there was a growth only to 10% (most likely related to the 20% human-led attacks on Telecoms in the same year).
The IT sector is stably affected by malware, but the share is small: the maximum was observed in 2020 (25%) and 2022 (14%). Subsequent years — the share of such attacks did not exceed one-tenth. After all, IT is compromised mainly not to encrypt, but to develop an attack through the supply chain. And that means attackers need to sit in the infrastructure as quietly and unnoticed as possible.
Curiously, malware attacks on MDR clients from the Media sector were not observed throughout the observation period, although in 2022, this sector was among the leaders in the share of human-driven attacks from the total number of critical incidents, second only to Telecoms. This is great, since detecting ransomware attacks at the late stage (active malware work without visible human participation) usually does not end with successful data recovery.
Transport companies are stably attacked by malware, the maximums were observed in 2022 (19%) and 2023 (22%). In the leading year of critical incidents, 2022, the share of malware attacks on Transport was comparable to that of Finance: 8% versus 6%.
Social Engineering#
We’ve already noted the connection between human-driven attacks and malware attacks: the latter most often occur when human work is already completed. Social engineering has been in the top-3 scenarios for initial access throughout our observation period. In general, a typical attack looks like this: Social Engineering ==> Human-Operated Stage ==> Damage using malware.
Within MDR, no heavy forensics is performed, so the detection of a malware incident is not always unwound to the stage of human operation, and even less often — to the social engineering stage; especially since the malware detection and initial access can be separated by many weeks. But we can imagine that incidents detected and prevented at the social engineering stage, if missed, could later be noticed as human-driven attacks, and in case of a miss here — it would lead to malware attacks, causing significant damage. Therefore, a hypothesis arises that if we notice more human-led attacks and malware, then less social engineering was detected previously, and vice versa.
And another hypothesis: periods with predominant social engineering attacks are followed by periods with a predominant number of human-driven and malware attacks, since some fishing attempts convert into success, and the more attempts, the higher the effectiveness.
To confirm these hypotheses, let’s consider the visualization of the distribution of social engineering by industry over the period from 2020 to 2025.
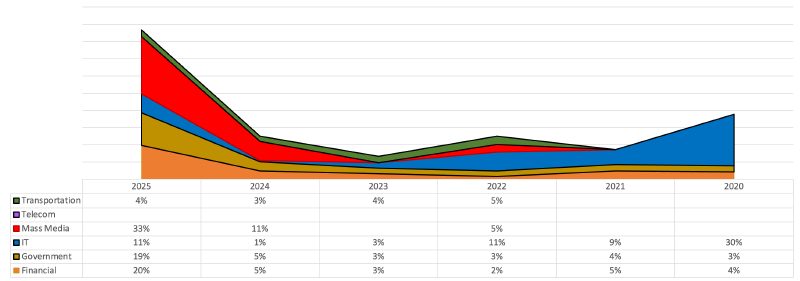
The share of human-driven and malware attacks in most cases indeed changes in antiphase to social engineering attacks. The exception is 2022, where everyone suffered from social engineering. And most of all — IT sector, but the share was relatively small: 11% of the total number of critical incidents.
But most of all, IT suffered in 2020 (30%), and then there was a decline to 1% in 2024. However, we noted a growth in the share of human-managed attacks in IT sector, up to 60% in 2024; this seems to confirm the hypothesis about the transformation of social engineering into human-led attacks over time.
In 2025, IT again saw a growth in social engineering from 1% to 11%, but the share of human-led attacks was also quite high — 41%. Perhaps the transition period from fishing to further attack development is shortening, and therefore the effectiveness and success of social engineering are growing.
In favor of the increase in the effectiveness of fishing, the overall significant growth in the share of such attacks across all sectors also testifies. After a brief lull in 2023, attackers again began to flood the Media with social engineering: in 2024, the share of fishing was 11%, and in 2025 — 33%, which gives reason to expect a growth in human-driven attacks on the Media in subsequent years.
Curiously, critical incidents related to successful social engineering were not observed in Telecoms, although human-driven attacks and malware were seen there; in 2021-22, Telecoms were among the leaders. Probably, initial access to Telecoms is obtained in a different way.
Conclusion#
The wide coverage of various sectors of the economy allows us to build hypotheses that are confirmed in practice, and the prolonged observation allows us to notice trends the period of which significantly exceeds one year.
We considered exclusively high-critical incidents, since the preparation and implementation of such attacks requires significant efforts from attackers, and therefore, the analysis of such incidents better reflects the most likely motivation of attackers.
Focus is the key to success, and this principle is not alien to attackers: in different years, we can observe the interest of attackers in different industries. The combination of data on the most attacked industries with the global situation explains the motivation of attackers: for example, attacks on the Media and Government in 2022 or attacks on Telecoms a year earlier.
Observing changes in the types of attacks and focus by industry allows us to identify recurring dependencies. For example, a surge in fishing attacks later transforms into human-driven attacks, which, in turn, develop into malware attacks to cause damage.
We can also see less noticeable (on short observation periods) trends, such as the shift in focus from Telecoms to IT sector, as confirmation of the growth of attacks on supply chains, in comparison with historically leading scenarios of exploiting trusted relationships.