A year ago, we reported how the credentials of thousands of Fortinet customers leaked online due to a vulnerability in the authentication system. And now, the security systems of the same company have proven to be not very secure again.
In December 2025, two vulnerabilities, CVE-2025-59718 and CVE-2025-59719, were discovered that allowed bypassing authentication in Fortinet products using the single sign-on (SSO) mechanism and the FortiCloud account. These vulnerabilities allowed attackers to authenticate using a specially crafted SAML packet sent to FortiOS, FortiWeb, FortiProxy, or FortiSwitch Manager if the SSO feature is enabled on the device.
Similar attacks bypassing SSO authentication were observed in Fortinet customers in January as well. This was a new vulnerability, CVE-2026-24858, and it also allowed an attacker with a FortiCloud account to log in to other people’s accounts in FortiOS, FortiManager, FortiAnalyzer, FortiProxy, and FortiWeb.
How to protect yourself:
Fortinet has disabled authentication via FortiCloud SSO for vulnerable product versions. Customers are advised to update these products to the patched versions, after that SSO authentication will work again. You can also disable SSO in your products manually – just in case a fourth vulnerability of the same type is found.
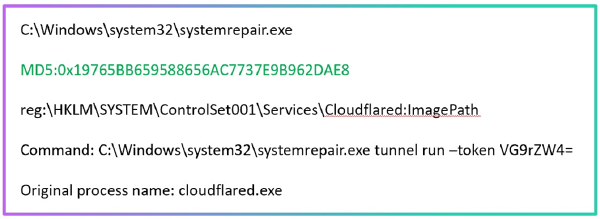
Exploitation attempts can be detected using indicators of compromise including FortiCloud accounts that were used for attacks, as well as the IP addresses of the attackers and the accounts that were created after successful attacks to maintain persistence.
In addition to IOCs, the attack is detected by distinctive actions after gaining access to the system: this includes exporting the system configuration and creating an administrative account for persistence.
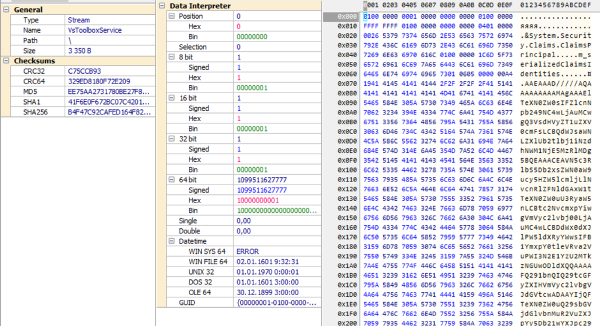
Telemetry can be collected from Fortinet products to detect this malicious activity:
— data on the account, IP address, and authentication method is available in authentication events (FTNTFGTmethod=sso or method=sso),
— information about the creation of an administrative account (msg=”Add system.admin …”),
— information about the export of the configuration (msg=”System config file has been downloaded by user …”).
Also, in January, almost simultaneously with the attacks on Fortinet, attackers compromised another security product: malicious software was distributed through the update server of the eScan antivirus. The moral of the story: you need to monitor all products, including those designed to ensure security.