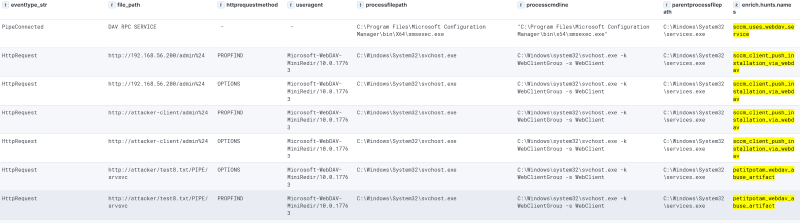
The WebClient service, which implements the WebDAV protocol in Windows, is of particular interest to attackers, as it allows relay attacks on other protocols (e.g., LDAPS), which in turn enables relaying to a domain controller.
In particular, an attacker can elevate privileges and even completely take over the domain, if the WebClient is installed on an SCCM server and the following conditions are met:
— either LDAP signing or LDAPS channel binding is disabled on at least one domain controller,
— automatic client push installation is enabled,
— NTLM Fallback is enabled.
The screenshot above shows a scenario for exploiting an SCCM server through client push installation. A similar picture will be seen in attacks on forced authentication (coerce).
How to protect yourself?
We recommend disabling the WebClient service on SCCM servers. If this is not possible, monitor suspicious WebDav protocol requests from the SCCM server.
To learn about other techniques for attacking System Center Configuration Manager (SCCM) and about methods for detecting those attacks, watch Alexander Rodchenko’s presentation: “C2 by Microsoft: What can go wrong if SCCM ends up in the wrong hands”.