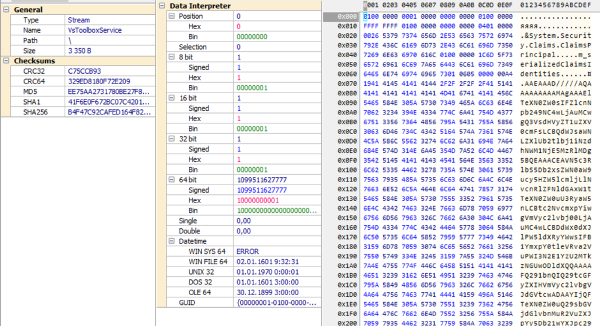
A technique much simpler than rootkit can make a malicious process invisible
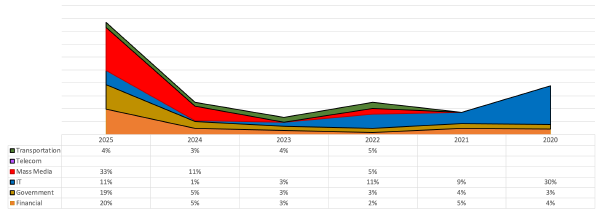
Combining MDR and IR statistics provides a better understanding of current and emerging threats
How our MDR team investigated a Brazilian hacker attack on Mexico
What types of attacks are leading in different sectors in different years?
How critical incidents of different types were distributed across industries in 2020-2025
Another story of non-standard remote access
Attackers used Velociraptor, VS Code Tunnel, Cloudflare Tunnel, and Zoho Assist
Attackers were distributing malware from Notepad++ update center
An attacker with a FortiCloud account can log in to other users’ FortiOS
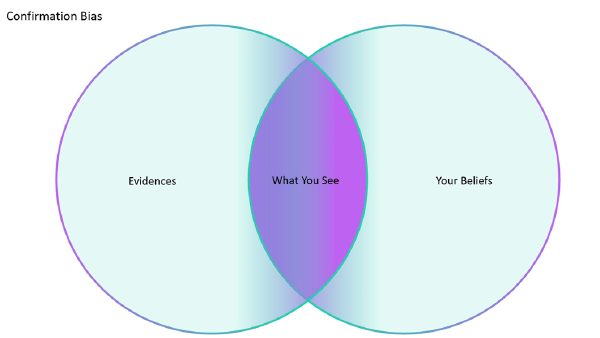
Anchoring effect, reasoning by analogy, and other logical errors
The most common biases that occur in SOC and how to avoid them
Built-in antivirus could be switched off without any third-party software
We selected posts that got the most likes
A new technique to exploit VS IDE using SUO files